Pursuit vs Threat Watch
Side-by-side comparison to help you choose the right product.
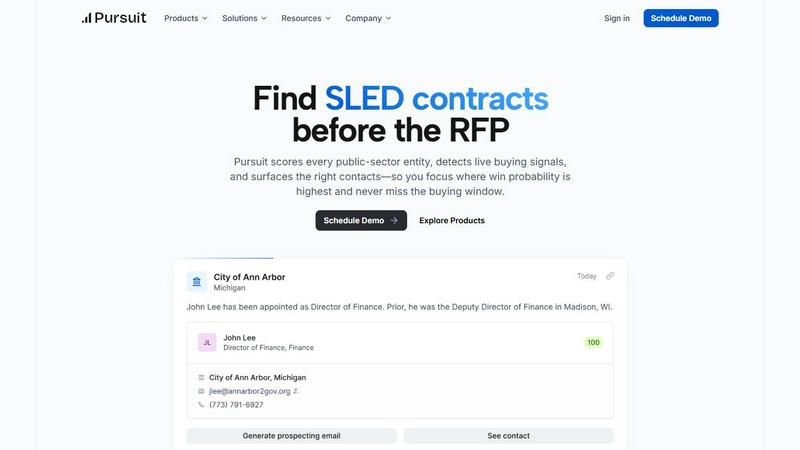
Pursuit
Pursuit uses AI to identify high-probability SLED sales opportunities before RFPs are issued.
Last updated: February 28, 2026
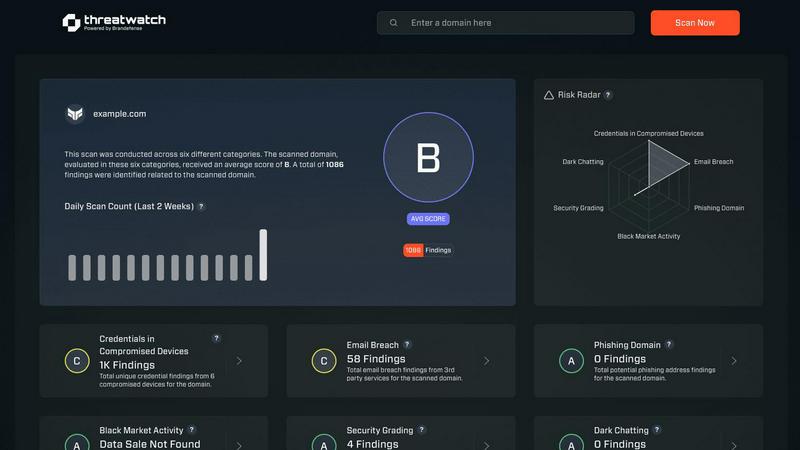
Threat Watch
Threat Watch provides rapid insights to evaluate and strengthen your cybersecurity posture across essential security.
Last updated: March 1, 2026
Visual Comparison
Pursuit
Threat Watch
Feature Comparison
Pursuit
Pre-RFP Signal Detection
Pursuit’s proprietary AI engine continuously monitors and analyzes public data sources from over 110,000 SLED entities to identify live buying signals. These signals, extracted from budget documents, meeting agendas, and contract postings, surface actionable opportunities 6 to 18 months before a formal Request for Proposal is released. This early intelligence allows sales teams to position themselves as informed partners rather than reactive bidders, fundamentally changing the entry point for SLED engagements.
Entity and Contact Database with Continuous Enrichment
The platform maintains a constantly updated database of over 90,000 entities and 4 million contacts within the SLED ecosystem. Pursuit ensures 94% data accuracy through automated, continuous enrichment, tracking organizational changes, role transitions, and new hires. This eliminates the fragility of static contact lists and personal networks, providing a single source of truth that persists despite staff turnover.
Native CRM and MarTech Integrations
Pursuit offers bi-directional synchronization with core go-to-market systems like Salesforce and HubSpot. Enriched account data, contact information, and identified buying signals flow automatically into these platforms, eliminating manual data entry and ensuring intelligence is actionable within existing workflows. This seamless integration is credited with reducing data enrichment time by 68% according to user case studies.
Role-Specific Intelligence Delivery
Intelligence is delivered through persona-specific interfaces. Account Executives receive instant meeting prep via a Chrome extension, BDRs get daily prioritized call lists, Marketing can build ABM campaigns around budget cycles, and Customer Success receives configurable renewal alerts. This ensures every team member gets the right information in the right format to drive their specific function, from prospecting to renewal.
Threat Watch
Comprehensive Security Analysis
Threat Watch provides an in-depth analysis of an organization's cybersecurity landscape. It evaluates critical security categories, ensuring users gain a holistic view of their security posture and can effectively identify vulnerabilities.
Real-Time Insights
With its real-time data monitoring capabilities, Threat Watch empowers organizations to stay ahead of potential threats. Users receive immediate alerts about security issues, allowing for timely responses to mitigate risks.
Automated Risk Assessments
The platform automates the process of risk assessments, significantly reducing the workload on cybersecurity teams. This feature enables organizations to conduct regular evaluations without extensive manual effort, ensuring continuous security oversight.
Dark Web Monitoring
Threat Watch actively monitors the dark web for compromised credentials and sensitive data. By identifying potential breaches and unauthorized access to information, organizations can take swift action to protect their assets.
Use Cases
Pursuit
Accelerating New Sales Pipeline Generation
Business Development Representatives use Pursuit to move beyond cold calling based on hunches. The platform provides daily, prioritized lists of accounts exhibiting concrete buying signals, such as recent budget approvals for relevant initiatives or upcoming contract expirations. This signal-driven approach has been shown to increase qualified SLED pipeline by 47% and achieve cold call conversion rates as high as 20%, according to published case studies.
Improving Account Executive Win Rates
Account Executives leverage Pursuit’s intelligence to prepare for meetings and craft compelling proposals. The Chrome extension provides immediate context on the account’s procurement history, incumbent vendors, contract values, and recent buying committee discussions. Showing up with this depth of knowledge builds credibility and allows AEs to tailor their solution effectively, leading to a documented 32% improvement in win rates.
Enabling Signal-Based Account-Based Marketing (ABM)
Marketing teams utilize Pursuit to build highly targeted ABM campaigns grounded in real-time intelligence. Instead of targeting accounts based on firmographics alone, they can create audiences based on active signals like new technology initiatives or leadership changes tied to budget cycles. Syncing these audiences to platforms like LinkedIn Ads and Marketo has resulted in a 2.4x lift in campaign conversion rates.
Proactive Customer Success and Renewal Management
Customer Success managers configure Pursuit to monitor their existing customer base for both renewal and churn signals. Alerts for contract expirations (90-180 days in advance), budget cuts, leadership changes, or competitor RFPs allow for proactive outreach and risk mitigation. This early signal identification enables teams to identify renewal opportunities 3x faster and protect revenue.
Threat Watch
Proactive Threat Detection
Organizations can utilize Threat Watch to implement proactive threat detection strategies. By regularly monitoring their digital assets, they can identify vulnerabilities before they are exploited, thereby enhancing their overall security.
Incident Response Planning
Threat Watch aids in developing effective incident response plans. By understanding the landscape of potential threats, organizations can prepare and implement strategies to minimize damage in the event of a cybersecurity incident.
Compliance and Regulatory Requirements
Many organizations face stringent compliance and regulatory requirements regarding data protection. Threat Watch helps ensure that organizations meet these requirements by providing comprehensive assessments of their cybersecurity health.
Enhanced Security Training
IT teams can leverage insights from Threat Watch to inform security training initiatives. By understanding the most common vulnerabilities and threats, organizations can better educate employees on best practices and security awareness.
Overview
About Pursuit
Pursuit is an AI-powered sales intelligence platform engineered specifically for businesses selling to state, local, and education (SLED) government entities. It directly addresses the unique and formidable challenges of public-sector sales, which include navigating over 110,000 distinct entities, complex procurement rules, and elongated budget cycles that can span fiscal years. The platform serves sales, business development, marketing, and customer success teams at government technology vendors, contractors, and consultants. Its core mission is to transform the traditionally opaque and relationship-dependent SLED market into a data-driven, proactive sales process. Pursuit achieves this by continuously analyzing public data from a vast network of entities and contacts, applying proprietary artificial intelligence to detect genuine buying signals from documents like budget approvals, council meeting minutes, and contract expirations—often 6-18 months before a formal RFP is issued. This pre-RFP intelligence allows teams to identify opportunities earlier, understand the procurement path, and engage with the right stakeholders at the optimal time. The platform's ultimate value proposition is a significant increase in win rates and pipeline velocity by ensuring sales efforts are focused on entities with the highest verified propensity to buy, effectively ensuring teams never miss the critical buying window.
About Threat Watch
Threat Watch is a cutting-edge cybersecurity intelligence solution designed to empower organizations by providing a comprehensive overview of their cyber health. This innovative tool meticulously analyzes an organization's digital assets, vulnerabilities, and exposures, enabling users to swiftly identify and address potential risks. By leveraging real-time insights and automated assessments, Threat Watch offers a clear picture of security threats, allowing businesses to prioritize and mitigate risks effectively. It is particularly beneficial for IT professionals, cybersecurity teams, and organizational leaders who seek to bolster their defenses against ever-evolving cyber threats. With its robust capabilities, Threat Watch not only uncovers critical security issues but also enhances the overall cybersecurity posture of any organization, making it an indispensable asset in today’s digital landscape. By focusing on essential security categories such as compromised credentials, breached accounts, and dark web content, Threat Watch ensures that organizations can respond proactively to cybersecurity challenges, ultimately safeguarding their operational integrity and protecting sensitive data.
Frequently Asked Questions
Pursuit FAQ
What types of buying signals does Pursuit detect?
Pursuit’s AI is trained to identify a wide range of non-RFP signals indicative of future procurement. This includes budget line-item approvals for specific projects, discussions in city council or school board meeting minutes, the expiration dates of existing vendor contracts, the posting of RFIs (Requests for Information), and leadership changes in relevant departments. These signals collectively paint a picture of budgetary intent and project planning long before a formal bid is solicited.
How does Pursuit ensure data accuracy and relevance?
The platform employs a multi-layered approach to data integrity. First, it aggregates data from primary, public sources. Second, proprietary AI and machine learning models clean, deduplicate, and contextualize this information. Third, continuous automated enrichment processes run to update records for contact changes, role transitions, and organizational updates. This results in a documented 94% data accuracy rate, ensuring teams are working with current and actionable intelligence.
Can Pursuit integrate with our existing tech stack (CRM, marketing automation)?
Yes, Pursuit is built with integration as a core principle. It offers native, bi-directional integrations with major CRM platforms like Salesforce and HubSpot, allowing enriched account/contact data and buying signals to sync automatically. For marketing teams, Pursuit can push segmented audiences and intent signals directly into platforms such as Marketo, HubSpot, and LinkedIn Campaign Manager, enabling seamless signal-based campaign execution.
Is Pursuit only for large enterprises selling to SLED?
No, Pursuit is designed for any business that sells products or services to state, local, or education government entities. This includes technology vendors of all sizes, contractors, consultants, and professional services firms. The platform is particularly valuable for companies looking to scale their SLED sales operations efficiently, as it reduces the heavy research burden and levels the playing field by providing intelligence that was previously only accessible through vast personal networks.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, including small businesses, large enterprises, and government agencies. Any entity that prioritizes cybersecurity can leverage its features to enhance their cyber health.
How does Threat Watch monitor the dark web?
Threat Watch employs advanced algorithms and data mining techniques to continuously scan the dark web for compromised accounts and credentials. This proactive monitoring helps organizations stay informed about potential threats to their data.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to complement existing cybersecurity solutions. Its integration capabilities allow organizations to enhance their security framework without disrupting current workflows.
Is Threat Watch easy to use for non-technical users?
Absolutely. Threat Watch features an intuitive user interface that makes it accessible to both technical and non-technical users. Comprehensive dashboards and reports simplify complex data, enabling informed decision-making for all stakeholders.
Alternatives
Pursuit Alternatives
Pursuit is an AI-powered sales intelligence platform within the business intelligence category, specifically designed for companies selling to state, local, and education (SLED) government agencies. It transforms the traditionally opaque public sector sales process by using artificial intelligence to detect early buying signals and prioritize high-probability opportunities, thereby increasing pipeline velocity and win rates. Users may explore alternatives to Pursuit for various reasons, including budget constraints, specific feature requirements not addressed by the platform, or a need for a different sales methodology. Some organizations might seek tools with a broader market focus beyond SLED, require deeper integration with a particular tech stack, or prefer a different pricing model, such as per-user subscriptions versus enterprise-wide contracts. When evaluating an alternative, key considerations should include the depth and accuracy of public sector data coverage, the sophistication of AI in identifying genuine buying intent, and the platform's ability to integrate actionable intelligence directly into existing CRM workflows. The ideal solution should demonstrably reduce time spent on manual research and provide clear, timely insights that enable sales teams to engage prospects proactively, well before a formal RFP is issued.
Threat Watch Alternatives
Threat Watch is a state-of-the-art cybersecurity intelligence solution that falls within the realm of business intelligence, specifically tailored to enhance an organization's cybersecurity health. This tool offers a comprehensive overview of digital assets, vulnerabilities, and exposures, enabling IT professionals and organizational leaders to quickly identify and mitigate potential risks. Users commonly seek alternatives to Threat Watch due to various factors, including pricing, feature sets, and specific platform needs that may not be fully addressed by the product. When considering alternatives, it's crucial to evaluate the capabilities of each solution, such as real-time risk assessments, automated vulnerability scanning, and comprehensive reporting, ensuring that they align with the unique security requirements of your organization. --- [{"question": "What is Threat Watch?", "answer": "Threat Watch is a cybersecurity intelligence solution that helps organizations assess and enhance their cybersecurity health by providing real-time insights into vulnerabilities and threats."},{"question": "Who is Threat Watch for?", "answer": "Threat Watch is designed for IT professionals, cybersecurity teams, and organizational leaders who aim to improve their defenses against evolving cyber threats."},{"question": "Is Threat Watch free?", "answer": "Threat Watch is a premium service, and pricing details can vary based on the specific needs and scale of the organization."},{"question": "What are the main features of Threat Watch?", "answer": "Main features of Threat Watch include real-time risk assessment, automated vulnerability scanning, dark web monitoring, and comprehensive reporting."}]
