Threat Watch
Threat Watch provides rapid insights to evaluate and strengthen your cybersecurity posture across essential security.
Visit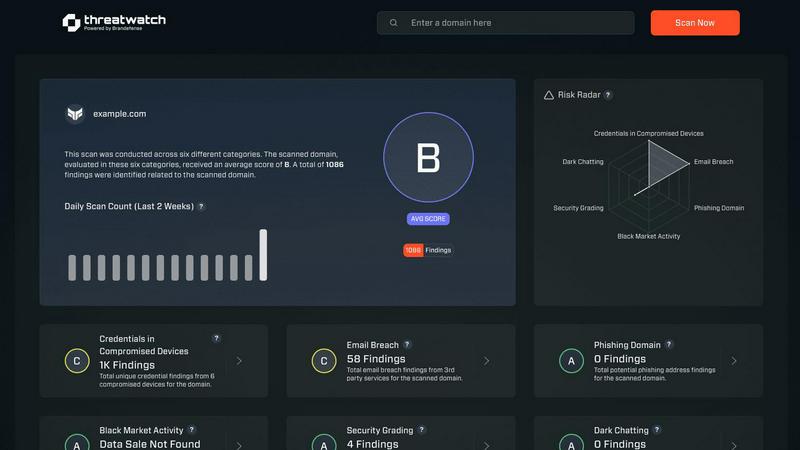
About Threat Watch
Threat Watch is a cutting-edge cybersecurity intelligence solution designed to empower organizations by providing a comprehensive overview of their cyber health. This innovative tool meticulously analyzes an organization's digital assets, vulnerabilities, and exposures, enabling users to swiftly identify and address potential risks. By leveraging real-time insights and automated assessments, Threat Watch offers a clear picture of security threats, allowing businesses to prioritize and mitigate risks effectively. It is particularly beneficial for IT professionals, cybersecurity teams, and organizational leaders who seek to bolster their defenses against ever-evolving cyber threats. With its robust capabilities, Threat Watch not only uncovers critical security issues but also enhances the overall cybersecurity posture of any organization, making it an indispensable asset in today’s digital landscape. By focusing on essential security categories such as compromised credentials, breached accounts, and dark web content, Threat Watch ensures that organizations can respond proactively to cybersecurity challenges, ultimately safeguarding their operational integrity and protecting sensitive data.
Features of Threat Watch
Comprehensive Security Analysis
Threat Watch provides an in-depth analysis of an organization's cybersecurity landscape. It evaluates critical security categories, ensuring users gain a holistic view of their security posture and can effectively identify vulnerabilities.
Real-Time Insights
With its real-time data monitoring capabilities, Threat Watch empowers organizations to stay ahead of potential threats. Users receive immediate alerts about security issues, allowing for timely responses to mitigate risks.
Automated Risk Assessments
The platform automates the process of risk assessments, significantly reducing the workload on cybersecurity teams. This feature enables organizations to conduct regular evaluations without extensive manual effort, ensuring continuous security oversight.
Dark Web Monitoring
Threat Watch actively monitors the dark web for compromised credentials and sensitive data. By identifying potential breaches and unauthorized access to information, organizations can take swift action to protect their assets.
Use Cases of Threat Watch
Proactive Threat Detection
Organizations can utilize Threat Watch to implement proactive threat detection strategies. By regularly monitoring their digital assets, they can identify vulnerabilities before they are exploited, thereby enhancing their overall security.
Incident Response Planning
Threat Watch aids in developing effective incident response plans. By understanding the landscape of potential threats, organizations can prepare and implement strategies to minimize damage in the event of a cybersecurity incident.
Compliance and Regulatory Requirements
Many organizations face stringent compliance and regulatory requirements regarding data protection. Threat Watch helps ensure that organizations meet these requirements by providing comprehensive assessments of their cybersecurity health.
Enhanced Security Training
IT teams can leverage insights from Threat Watch to inform security training initiatives. By understanding the most common vulnerabilities and threats, organizations can better educate employees on best practices and security awareness.
Frequently Asked Questions
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, including small businesses, large enterprises, and government agencies. Any entity that prioritizes cybersecurity can leverage its features to enhance their cyber health.
How does Threat Watch monitor the dark web?
Threat Watch employs advanced algorithms and data mining techniques to continuously scan the dark web for compromised accounts and credentials. This proactive monitoring helps organizations stay informed about potential threats to their data.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to complement existing cybersecurity solutions. Its integration capabilities allow organizations to enhance their security framework without disrupting current workflows.
Is Threat Watch easy to use for non-technical users?
Absolutely. Threat Watch features an intuitive user interface that makes it accessible to both technical and non-technical users. Comprehensive dashboards and reports simplify complex data, enabling informed decision-making for all stakeholders.
Explore more in this category:
Similar to Threat Watch
Generate unique and memorable business names instantly with our AI Business Name Generator, perfect for startups and brands.
MarketWrk automates CPG pricing, MAP monitoring, and review alerts, transforming raw data into actionable insights for your team.
Opal44 uses AI to explain your Google Analytics data in clear, actionable English.
Fusedash is an AI-powered platform that transforms raw data into actionable dashboards and charts for instant team.
finban empowers you to confidently manage liquidity, forecast scenarios, and streamline budgeting in one intuitive.
Zignt streamlines contract signing and management with AI, ensuring secure, fast, and legally binding agreements for.
aVenture is an AI-powered platform delivering institutional-grade research on private companies and venture capital.
iGPT is an enterprise API that transforms email data into secure, contextual insights for agents.
