Karolium vs Threat Watch
Side-by-side comparison to help you choose the right product.
Karolium is a Gartner-recognized zero-code platform that accelerates digital transformation by building custom.
Last updated: February 28, 2026
Threat Watch
Threat Watch provides rapid insights to evaluate and strengthen your cybersecurity posture across essential security.
Last updated: March 1, 2026
Visual Comparison
Karolium

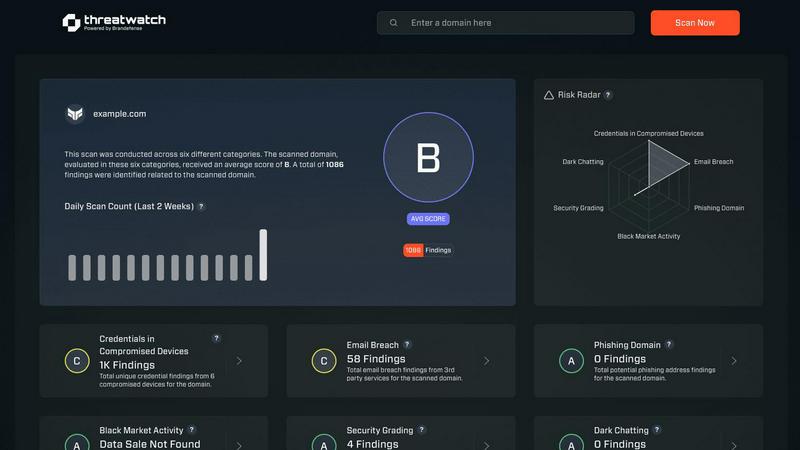
Threat Watch
Feature Comparison
Karolium
Unified Zero-Code Platform
Karolium integrates iPaaS, aPaaS, oPaaS, and AIPaaS into a single codeless environment. This eliminates dependency on specialized developers, allowing business analysts and process experts to visually design, customize, and deploy applications. Research by Forrester highlights that low-code/no-code platforms can reduce development time by 50-90%, a principle Karolium embodies by enabling rapid customization and extension of business solutions without writing a single line of code, thus accelerating time-to-value.
Pre-Composed Value Chain Modules
The platform offers a suite of enterprise-grade, ready-to-deploy modules targeting specific business functions, such as Supplier Collaboration, Unified Master Data Management, and AI-Infused Demand Forecasting. These are not rigid applications but composable building blocks. According to Gartner's principles of composability, this allows organizations to assemble and reconfigure business capabilities as needed, providing the flexibility to support unique workflows without costly point-to-point integrations or vendor lock-in.
Built-In Predictive & Prescriptive AI
Karolium is an enterprise intelligence platform with native AI capabilities. It goes beyond basic automation to offer built-in predictive analytics (e.g., for lead time or demand) and prescriptive solutions that recommend optimal actions. This embedded AI, accessible in a code-free environment, lowers the barrier to AI adoption, allowing companies to create intelligent applications that drive proactive decision-making, a capability IDC notes is critical for competitive advantage in modern supply chains.
Managed PaaS-Driven SaaS Delivery
Delivered as a managed Platform-as-a-Service-driven Software-as-a-Service, Karolium ensures organizations always have access to the latest platform capabilities and quarterly module enhancements without managing underlying infrastructure. This model, recognized for reducing IT overhead, provides boundless customization for both pre-packaged and user-composed modules and supports unlimited users, offering scalability and continuous innovation as a core service feature.
Threat Watch
Comprehensive Security Analysis
Threat Watch provides an in-depth analysis of an organization's cybersecurity landscape. It evaluates critical security categories, ensuring users gain a holistic view of their security posture and can effectively identify vulnerabilities.
Real-Time Insights
With its real-time data monitoring capabilities, Threat Watch empowers organizations to stay ahead of potential threats. Users receive immediate alerts about security issues, allowing for timely responses to mitigate risks.
Automated Risk Assessments
The platform automates the process of risk assessments, significantly reducing the workload on cybersecurity teams. This feature enables organizations to conduct regular evaluations without extensive manual effort, ensuring continuous security oversight.
Dark Web Monitoring
Threat Watch actively monitors the dark web for compromised credentials and sensitive data. By identifying potential breaches and unauthorized access to information, organizations can take swift action to protect their assets.
Use Cases
Karolium
Augmenting Legacy ERP Systems
Enterprises often find their core ERP systems lack flexibility for specific departmental workflows. Karolium enables businesses to seamlessly integrate with and extend legacy ERP and other systems. For instance, a company can use Karolium's modules to build a tailored supplier portal or a custom contract manufacturing dashboard that pulls data from the ERP, enhancing functionality without a risky and expensive core system replacement.
Rapid Deployment of Supply Chain Solutions
Organizations facing volatile markets need agile supply chain tools. Karolium allows for the rapid composition and deployment of solutions like centralized procurement hubs or smart warehousing applications. By using pre-built modules for appointment scheduling, yard management, and real-time collaboration, companies can deploy a cohesive supply chain control tower in weeks, not years, improving responsiveness and coordination.
Building AI-Driven Operational Applications
A manufacturing firm seeking to predict machine failure can use Karolium's AIPaaS capabilities to create an AI-infused asset monitoring application. Without needing a data science team, users can leverage built-in AI models for predictive maintenance, integrate IoT data streams, and create a digital twin simulation—all within the same zero-code platform, turning data into actionable prescriptive insights for maintenance teams.
Creating Unified Customer-Centric Portals
Businesses aiming to improve customer or partner experience can use Karolium to unify disparate data sources into a single, branded portal. For example, a company can compose a portal that provides clients with real-time order status, inventory levels, and AI-driven delivery forecasts by connecting CRM, OMS, and logistics systems. This enhances transparency and collaboration without complex, custom-coded integration projects.
Threat Watch
Proactive Threat Detection
Organizations can utilize Threat Watch to implement proactive threat detection strategies. By regularly monitoring their digital assets, they can identify vulnerabilities before they are exploited, thereby enhancing their overall security.
Incident Response Planning
Threat Watch aids in developing effective incident response plans. By understanding the landscape of potential threats, organizations can prepare and implement strategies to minimize damage in the event of a cybersecurity incident.
Compliance and Regulatory Requirements
Many organizations face stringent compliance and regulatory requirements regarding data protection. Threat Watch helps ensure that organizations meet these requirements by providing comprehensive assessments of their cybersecurity health.
Enhanced Security Training
IT teams can leverage insights from Threat Watch to inform security training initiatives. By understanding the most common vulnerabilities and threats, organizations can better educate employees on best practices and security awareness.
Overview
About Karolium
Karolium is a Gartner and IDC-recognized, next-generation enterprise platform designed to accelerate digital transformation by unifying multiple "as-a-Service" capabilities into a single, zero-code environment. It functions as a holistic iPaaS (Integration Platform as a Service), aPaaS (Application Platform as a Service), oPaaS (Operations Platform as a Service), and AIPaaS (AI Platform as a Service). This unified approach empowers businesses, particularly those in complex supply chain and operational landscapes, to rapidly build, extend, and customize intelligent business solutions without traditional coding. The platform directly addresses critical enterprise challenges such as the high cost and slow pace of custom software development, the inflexibility of off-the-shelf applications, and the complexity of adopting AI. By leveraging Karolium's library of ready-to-use, pre-composed modules and its completely composable architecture, organizations can augment their existing application ecosystems, create tailored workflows, and deploy AI-driven applications at reported speeds up to 10 times faster than conventional methods. Its core value proposition lies in delivering agility, operational efficiency, and embedded intelligence—enabling predictive and prescriptive capabilities—through a managed PaaS-driven SaaS model that ensures continuous updates and unlimited user scalability.
About Threat Watch
Threat Watch is a cutting-edge cybersecurity intelligence solution designed to empower organizations by providing a comprehensive overview of their cyber health. This innovative tool meticulously analyzes an organization's digital assets, vulnerabilities, and exposures, enabling users to swiftly identify and address potential risks. By leveraging real-time insights and automated assessments, Threat Watch offers a clear picture of security threats, allowing businesses to prioritize and mitigate risks effectively. It is particularly beneficial for IT professionals, cybersecurity teams, and organizational leaders who seek to bolster their defenses against ever-evolving cyber threats. With its robust capabilities, Threat Watch not only uncovers critical security issues but also enhances the overall cybersecurity posture of any organization, making it an indispensable asset in today’s digital landscape. By focusing on essential security categories such as compromised credentials, breached accounts, and dark web content, Threat Watch ensures that organizations can respond proactively to cybersecurity challenges, ultimately safeguarding their operational integrity and protecting sensitive data.
Frequently Asked Questions
Karolium FAQ
What is a "unified zero-code platform"?
A unified zero-code platform combines multiple cloud platform services—like integration, application development, operations, and AI—into a single environment where users can build and modify software using visual tools and configuration instead of traditional programming. Karolium unifies iPaaS, aPaaS, oPaaS, and AIPaaS, meaning you can integrate systems, build apps, manage operations, and embed AI all through a drag-and-drop, codeless interface, significantly simplifying and accelerating digital project delivery.
How does Karolium address the limitations of off-the-shelf software?
Off-the-shelf software often forces businesses to adapt their processes to the software's limitations. Karolium's composable architecture, with its pre-built but flexible modules, allows organizations to tailor solutions to their exact workflows. You can extend, modify, and connect these modules to create a perfect fit for your operations, thereby overcoming the rigidity of standard packages while avoiding the high cost and long timelines of fully custom-coded alternatives.
Can Karolium integrate with our existing systems?
Yes, seamless integration is a core capability. As an Integration Platform as a Service (iPaaS), Karolium is designed to connect with a wide array of legacy systems, modern microservices applications, databases, and cloud services. This ensures you can augment your current application ecosystem without needing to replace it, creating a connected digital fabric that leverages existing investments while adding new, intelligent functionality.
What kind of AI capabilities does Karolium offer?
Karolium offers both predictive and prescriptive AI capabilities built directly into the platform. This includes pre-composed solutions like AI-infused demand forecasting, lead time prediction, and image recognition automation. Furthermore, its AIPaaS environment provides a flexible, code-free toolkit for creating custom AI-driven business applications, making advanced analytics and machine learning accessible to business users without deep technical expertise in data science.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, including small businesses, large enterprises, and government agencies. Any entity that prioritizes cybersecurity can leverage its features to enhance their cyber health.
How does Threat Watch monitor the dark web?
Threat Watch employs advanced algorithms and data mining techniques to continuously scan the dark web for compromised accounts and credentials. This proactive monitoring helps organizations stay informed about potential threats to their data.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to complement existing cybersecurity solutions. Its integration capabilities allow organizations to enhance their security framework without disrupting current workflows.
Is Threat Watch easy to use for non-technical users?
Absolutely. Threat Watch features an intuitive user interface that makes it accessible to both technical and non-technical users. Comprehensive dashboards and reports simplify complex data, enabling informed decision-making for all stakeholders.
Alternatives
Karolium Alternatives
Karolium is a unified zero-code platform in the application development category, designed to help businesses build custom applications and extend their digital ecosystems without traditional programming. It emphasizes rapid deployment, AI-driven analytics, and seamless integration with existing systems. Users often explore alternatives to platforms like Karolium for several key reasons. These can include budget constraints and specific pricing model needs, a requirement for different feature sets or deeper customization in certain areas, and the necessity to align with an organization's existing technology stack and long-term strategic platform requirements. When evaluating an alternative, it is crucial to assess the platform's core capabilities against your primary use cases. Key considerations should include the true extent of its customization and integration abilities, the sophistication of its built-in analytics and intelligence features, and the total cost of ownership, including scalability and support structures. The goal is to find a solution that balances power with usability to drive genuine digital transformation.
Threat Watch Alternatives
Threat Watch is a state-of-the-art cybersecurity intelligence solution that falls within the realm of business intelligence, specifically tailored to enhance an organization's cybersecurity health. This tool offers a comprehensive overview of digital assets, vulnerabilities, and exposures, enabling IT professionals and organizational leaders to quickly identify and mitigate potential risks. Users commonly seek alternatives to Threat Watch due to various factors, including pricing, feature sets, and specific platform needs that may not be fully addressed by the product. When considering alternatives, it's crucial to evaluate the capabilities of each solution, such as real-time risk assessments, automated vulnerability scanning, and comprehensive reporting, ensuring that they align with the unique security requirements of your organization. --- [{"question": "What is Threat Watch?", "answer": "Threat Watch is a cybersecurity intelligence solution that helps organizations assess and enhance their cybersecurity health by providing real-time insights into vulnerabilities and threats."},{"question": "Who is Threat Watch for?", "answer": "Threat Watch is designed for IT professionals, cybersecurity teams, and organizational leaders who aim to improve their defenses against evolving cyber threats."},{"question": "Is Threat Watch free?", "answer": "Threat Watch is a premium service, and pricing details can vary based on the specific needs and scale of the organization."},{"question": "What are the main features of Threat Watch?", "answer": "Main features of Threat Watch include real-time risk assessment, automated vulnerability scanning, dark web monitoring, and comprehensive reporting."}]