iGPT vs Threat Watch
Side-by-side comparison to help you choose the right product.
iGPT is an enterprise API that transforms email data into secure, contextual insights for agents.
Last updated: March 1, 2026
Threat Watch
Threat Watch provides rapid insights to evaluate and strengthen your cybersecurity posture across essential security.
Last updated: March 1, 2026
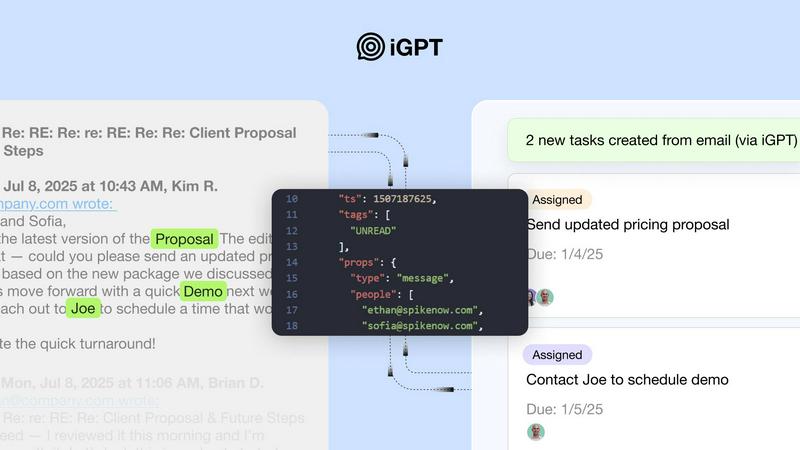
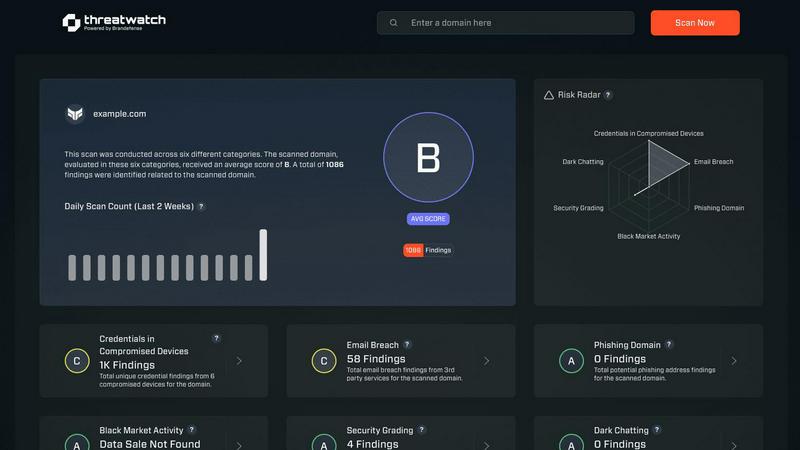
Visual Comparison
iGPT
Threat Watch
Feature Comparison
iGPT
Unified Intelligence Endpoint
iGPT consolidates the entire process of email intelligence into a single API call. This eliminates the need for developers to build and maintain separate systems for retrieval, context shaping, and reasoning, a common challenge noted in complex RAG implementations. A user simply submits a natural language query, and the API handles deep indexing, hybrid retrieval, and optimized context preparation automatically, returning a structured response with citations in approximately 3 seconds to the first token.
Deep Contextual Understanding & Thread Reconstruction
The API goes beyond simple keyword matching by semantically understanding email content and its relational context. It automatically reconstructs fragmented email threads across time, participants, and related attachments, rebuilding the complete narrative of a conversation. This capability is crucial for accurate understanding, as critical information is often distributed across multiple messages and replies, a nuance that standard search fails to capture.
Advanced Attachment Processing
iGPT extracts and indexes text, data, and structural information from a wide array of attachments, including documents, PDFs, and spreadsheets. This processing is performed in the context of the surrounding email thread and its participants, allowing the system to answer questions about contract clauses, invoice details, or report figures as they were discussed, turning static files into queryable knowledge assets.
Enterprise-Grade Security & Compliance Framework
Built for regulated industries, iGPT enforces a strict security model. It guarantees zero data training or retention, with all inferences processed in memory. Access is controlled via OAuth-only processing with Role-Based Access Control (RBAC), and every response includes a full audit trail, linking answers directly to source messages. This ensures data sovereignty and compliance with stringent data protection standards.
Threat Watch
Comprehensive Security Analysis
Threat Watch provides an in-depth analysis of an organization's cybersecurity landscape. It evaluates critical security categories, ensuring users gain a holistic view of their security posture and can effectively identify vulnerabilities.
Real-Time Insights
With its real-time data monitoring capabilities, Threat Watch empowers organizations to stay ahead of potential threats. Users receive immediate alerts about security issues, allowing for timely responses to mitigate risks.
Automated Risk Assessments
The platform automates the process of risk assessments, significantly reducing the workload on cybersecurity teams. This feature enables organizations to conduct regular evaluations without extensive manual effort, ensuring continuous security oversight.
Dark Web Monitoring
Threat Watch actively monitors the dark web for compromised credentials and sensitive data. By identifying potential breaches and unauthorized access to information, organizations can take swift action to protect their assets.
Use Cases
iGPT
Intelligent Email Assistants & Copilots
Organizations can build AI agents that draft, prioritize, summarize, and act on email with full historical and contextual awareness. For support teams, this means a copilot that can instantly reconstruct a customer's entire issue history across long email chains and attachments, enabling faster, more informed responses and reducing handle times significantly.
Automated Workflow & Task Orchestration
iGPT automates the extraction of actionable items from communication streams. It can automatically parse email threads to identify decisions, action items, owners, and deadlines, then feed this structured data into project management tools like Asana or Jira. This transforms unstructured conversations into tracked tasks and approvals, flagging stalled items for follow-up.
CRM Enrichment & Deal Intelligence
Sales and account management teams can use iGPT to extract critical deal momentum, customer sentiment, and decision rationale directly from email exchanges. The API can summarize key points from lengthy negotiation threads or identify all pending approvals mentioned in communications with a client, providing real-time insights that keep CRM data accurate and actionable.
Compliance Auditing & Legal Discovery
For legal, finance, and compliance departments, iGPT provides a powerful tool for tracing feedback, approvals, and contractual agreements back to their original source emails and attachments. This creates a verifiable audit trail, streamlining internal reviews, e-discovery processes, and ensuring that corporate decisions are fully documented and easily retrievable.
Threat Watch
Proactive Threat Detection
Organizations can utilize Threat Watch to implement proactive threat detection strategies. By regularly monitoring their digital assets, they can identify vulnerabilities before they are exploited, thereby enhancing their overall security.
Incident Response Planning
Threat Watch aids in developing effective incident response plans. By understanding the landscape of potential threats, organizations can prepare and implement strategies to minimize damage in the event of a cybersecurity incident.
Compliance and Regulatory Requirements
Many organizations face stringent compliance and regulatory requirements regarding data protection. Threat Watch helps ensure that organizations meet these requirements by providing comprehensive assessments of their cybersecurity health.
Enhanced Security Training
IT teams can leverage insights from Threat Watch to inform security training initiatives. By understanding the most common vulnerabilities and threats, organizations can better educate employees on best practices and security awareness.
Overview
About iGPT
iGPT is an advanced email intelligence API engineered to transform unstructured email data into structured, actionable insights for enterprise workflows and AI agents. It directly addresses the critical gap where traditional AI models fail: understanding the complex, contextual, and often messy nature of real-world email communication, which includes long threads, multiple participants, and diverse attachments. The platform serves a diverse range of industries, including customer support, legal, finance, and operations, by providing a secure, auditable gateway for AI systems to access and comprehend email data. Its core value proposition lies in its unified endpoint that replaces the need for complex, multi-step retrieval-augmented generation (RAG) pipelines. Organizations can bypass the burdens of parsing, chunking, indexing, and prompt tuning, instead sending a single natural language request to receive a context-aware, cited answer in seconds. With a foundational commitment to security—featuring zero data training, zero data retention, and full audit trails—iGPT empowers teams to automate tasks, enhance decision-making, and build sophisticated agents that operate with the full context of an organization's communication history.
About Threat Watch
Threat Watch is a cutting-edge cybersecurity intelligence solution designed to empower organizations by providing a comprehensive overview of their cyber health. This innovative tool meticulously analyzes an organization's digital assets, vulnerabilities, and exposures, enabling users to swiftly identify and address potential risks. By leveraging real-time insights and automated assessments, Threat Watch offers a clear picture of security threats, allowing businesses to prioritize and mitigate risks effectively. It is particularly beneficial for IT professionals, cybersecurity teams, and organizational leaders who seek to bolster their defenses against ever-evolving cyber threats. With its robust capabilities, Threat Watch not only uncovers critical security issues but also enhances the overall cybersecurity posture of any organization, making it an indispensable asset in today’s digital landscape. By focusing on essential security categories such as compromised credentials, breached accounts, and dark web content, Threat Watch ensures that organizations can respond proactively to cybersecurity challenges, ultimately safeguarding their operational integrity and protecting sensitive data.
Frequently Asked Questions
iGPT FAQ
How does iGPT's performance compare to building a custom RAG pipeline?
iGPT is designed to outperform and simplify custom RAG pipelines. While a custom pipeline requires significant engineering effort for parsing, chunking, embedding, vector store management, and prompt optimization, iGPT delivers a production-ready solution through a single API call. Benchmarks indicate it provides ~200ms retrieval and ~3s to first token across large email datasets, a performance level that typically requires extensive tuning in a custom setup.
What makes email a uniquely difficult data source for AI?
Email is inherently unstructured, conversational, and context-dependent. Critical information is dispersed across long threads with multiple participants, nested replies, and various file attachments. Traditional AI and search tools struggle with thread reconstruction, understanding tone shifts, and connecting data in attachments to the discussion about them. iGPT is specifically engineered to solve these "last-mile" context problems that break general-purpose LLMs.
Is my company's email data secure and private with iGPT?
Yes, iGPT is built with a foundational principle of data security. It employs a zero-data retention policy, meaning your inputs, prompts, and outputs are never stored after processing. The company also adheres to a strict zero-data training policy, ensuring your proprietary communications are never used to train or improve any AI models. All access is governed by OAuth and RBAC, keeping data under your organization's control.
How quickly can I integrate iGPT and start getting value?
Integration is designed for immediacy. iGPT provides a live playground for testing, comprehensive SDKs (including Python), and connectors for platforms like LangChain. Developers can connect email sources, test queries with different Context Engineering Framework (CEF) tiers, and receive structured, cited answers without any upfront data pipeline development, allowing teams to prototype and ship agents in days, not months.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, including small businesses, large enterprises, and government agencies. Any entity that prioritizes cybersecurity can leverage its features to enhance their cyber health.
How does Threat Watch monitor the dark web?
Threat Watch employs advanced algorithms and data mining techniques to continuously scan the dark web for compromised accounts and credentials. This proactive monitoring helps organizations stay informed about potential threats to their data.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to complement existing cybersecurity solutions. Its integration capabilities allow organizations to enhance their security framework without disrupting current workflows.
Is Threat Watch easy to use for non-technical users?
Absolutely. Threat Watch features an intuitive user interface that makes it accessible to both technical and non-technical users. Comprehensive dashboards and reports simplify complex data, enabling informed decision-making for all stakeholders.
Alternatives
iGPT Alternatives
iGPT is an advanced email intelligence API that falls within the Business Intelligence category. It specializes in transforming enterprise email data into secure, contextual insights to streamline agent workflows and automate decision-making processes. By providing a secure gateway for AI agents to understand email conversations and attachments, it helps organizations unlock the operational value of their communication data. Users may explore alternatives to iGPT for various reasons. Common drivers include budget constraints and specific pricing model needs, the requirement for different feature sets or integration capabilities with other platforms, and the desire for a solution tailored to a particular industry use case or company size. Evaluating the total cost of ownership and specific functional requirements is a standard part of the enterprise software selection process. When assessing an alternative email intelligence solution, key considerations should include the depth and security of its email data processing, the accuracy and contextual awareness of its AI responses, and the ease of integration into existing tech stacks. Compliance with data governance standards and the solution's ability to provide auditable, traceable insights are also critical factors for enterprise adoption, as noted in industry analyses of AI-powered workflow tools.
Threat Watch Alternatives
Threat Watch is a state-of-the-art cybersecurity intelligence solution that falls within the realm of business intelligence, specifically tailored to enhance an organization's cybersecurity health. This tool offers a comprehensive overview of digital assets, vulnerabilities, and exposures, enabling IT professionals and organizational leaders to quickly identify and mitigate potential risks. Users commonly seek alternatives to Threat Watch due to various factors, including pricing, feature sets, and specific platform needs that may not be fully addressed by the product. When considering alternatives, it's crucial to evaluate the capabilities of each solution, such as real-time risk assessments, automated vulnerability scanning, and comprehensive reporting, ensuring that they align with the unique security requirements of your organization. --- [{"question": "What is Threat Watch?", "answer": "Threat Watch is a cybersecurity intelligence solution that helps organizations assess and enhance their cybersecurity health by providing real-time insights into vulnerabilities and threats."},{"question": "Who is Threat Watch for?", "answer": "Threat Watch is designed for IT professionals, cybersecurity teams, and organizational leaders who aim to improve their defenses against evolving cyber threats."},{"question": "Is Threat Watch free?", "answer": "Threat Watch is a premium service, and pricing details can vary based on the specific needs and scale of the organization."},{"question": "What are the main features of Threat Watch?", "answer": "Main features of Threat Watch include real-time risk assessment, automated vulnerability scanning, dark web monitoring, and comprehensive reporting."}]