Deeploy vs Threat Watch
Side-by-side comparison to help you choose the right product.

Deeploy
Deeploy provides the essential governance infrastructure to manage AI risk and ensure compliance at scale.
Last updated: March 1, 2026
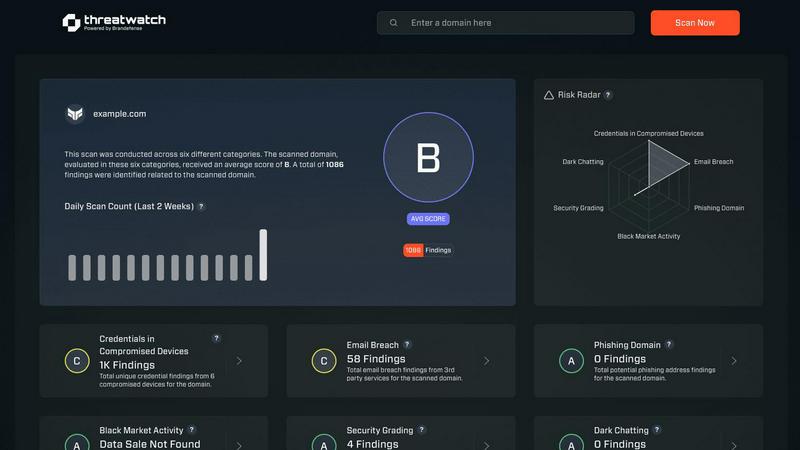
Threat Watch
Threat Watch provides rapid insights to evaluate and strengthen your cybersecurity posture across essential security.
Last updated: March 1, 2026
Visual Comparison
Deeploy
Threat Watch
Feature Comparison
Deeploy
AI Discovery and Onboarding
Deeploy provides complete visibility across an organization's AI landscape. It allows teams to discover, onboard, and manage every AI system—whether built on MLOps platforms, GenAI tools, or embedded systems—from a centralized dashboard. This eliminates blind spots and creates a single source of truth for all AI assets without requiring costly migration from existing platforms. The flexible onboarding process ensures that even disparate AI implementations can be brought under unified governance, establishing the foundational inventory required for effective oversight and compliance documentation.
Control Frameworks and Compliance
The platform simplifies navigating complex AI regulations through guided workflows and pre-built control frameworks. Organizations can adopt default frameworks aligned with major standards like ISO 42001 and the NIST AI Risk Management Framework (RMF) or build custom ones tailored to internal policies. Deeploy enables rapid AI system risk classification and establishes clear accountability with structured approval processes. This feature demystifies compliance, turning what is often a manual, legal-heavy burden into a streamlined, manageable operational procedure, directly addressing mandates like the EU AI Act.
Control Implementation and Automation
Deeploy translates high-level governance policies into enforceable, engineer-friendly controls. It automatically assigns the correct requirements to each AI system based on its risk profile, giving technical teams clear and actionable tasks. The platform accelerates compliance by up to 90% through the use of templates and automated evidence collection, reducing manual documentation work. Furthermore, it employs AI-powered assessments to handle repetitive compliance checks, ensuring governance is consistently applied and actually followed by engineering teams rather than being a bureaucratic hurdle.
Real-Time Monitoring and Explainability
This feature provides proactive oversight of AI systems in production. Deeploy monitors model performance, data drift, and output anomalies in real-time, sending instant alerts to prevent incidents before they impact users or create compliance breaches. It adds crucial tracing and guardrails to protect Large Language Model (LLM) outputs. Integrated explainability tools, such as feature contribution analysis, make AI decisions interpretable for both technical and non-technical stakeholders, building transparency and enabling effective human feedback loops to ensure safe and responsible AI operation.
Threat Watch
Comprehensive Security Analysis
Threat Watch provides an in-depth analysis of an organization's cybersecurity landscape. It evaluates critical security categories, ensuring users gain a holistic view of their security posture and can effectively identify vulnerabilities.
Real-Time Insights
With its real-time data monitoring capabilities, Threat Watch empowers organizations to stay ahead of potential threats. Users receive immediate alerts about security issues, allowing for timely responses to mitigate risks.
Automated Risk Assessments
The platform automates the process of risk assessments, significantly reducing the workload on cybersecurity teams. This feature enables organizations to conduct regular evaluations without extensive manual effort, ensuring continuous security oversight.
Dark Web Monitoring
Threat Watch actively monitors the dark web for compromised credentials and sensitive data. By identifying potential breaches and unauthorized access to information, organizations can take swift action to protect their assets.
Use Cases
Deeploy
Regulatory Compliance for Financial Services
Financial institutions use Deeploy to achieve and demonstrate compliance with stringent regulations like the EU AI Act and internal risk mandates. The platform's centralized registry and automated evidence collection provide auditors with a clear, documented trail of all AI systems, their risk classifications, and the controls in place. This is critical for high-stakes use cases like credit scoring or fraud detection, where explainability and auditability are non-negotiable for both regulators and customer trust.
Scalable AI Governance in Healthcare
Healthcare providers and digital health platforms leverage Deeploy to govern AI used in patient diagnostics, treatment recommendations, and mental health support. The platform's real-time monitoring and built-in explainability are crucial for clinical oversight, allowing medical professionals to understand AI-driven insights. The human feedback loop feature enables continuous improvement and validation of models, ensuring AI tools are safe, effective, and ethically deployed within sensitive care environments.
Centralized AI Oversight for Enterprise IT
Large enterprises with AI scattered across multiple business units and vendor platforms use Deeploy to regain control. The AI discovery capability maps all active systems, while the unified dashboard gives CIOs and heads of AI complete visibility into performance, costs, and risks. This central oversight prevents shadow IT, optimizes resource allocation, and ensures all AI initiatives align with corporate governance standards, enabling scalable and secure AI adoption across the organization.
Accelerating Model Deployment and MLOps
Data science and MLOps teams utilize Deeploy to streamline the path from development to production. The platform simplifies model deployment, reducing the process from weeks to hours. Once deployed, it provides continuous observability with performance dashboards and explainability reports. This not only accelerates innovation cycles but also bridges the gap between technical teams and business stakeholders by making model behavior transparent and actionable for continuous improvement.
Threat Watch
Proactive Threat Detection
Organizations can utilize Threat Watch to implement proactive threat detection strategies. By regularly monitoring their digital assets, they can identify vulnerabilities before they are exploited, thereby enhancing their overall security.
Incident Response Planning
Threat Watch aids in developing effective incident response plans. By understanding the landscape of potential threats, organizations can prepare and implement strategies to minimize damage in the event of a cybersecurity incident.
Compliance and Regulatory Requirements
Many organizations face stringent compliance and regulatory requirements regarding data protection. Threat Watch helps ensure that organizations meet these requirements by providing comprehensive assessments of their cybersecurity health.
Enhanced Security Training
IT teams can leverage insights from Threat Watch to inform security training initiatives. By understanding the most common vulnerabilities and threats, organizations can better educate employees on best practices and security awareness.
Overview
About Deeploy
Deeploy is an advanced AI governance and risk management platform designed to provide organizations with centralized oversight, compliance, and monitoring for their entire artificial intelligence portfolio. As AI systems proliferate across models, vendors, and embedded applications, they create a fragmented landscape fraught with operational blind spots and regulatory risks. Deeploy addresses this critical gap by serving as the essential governance infrastructure for the modern AI stack. It enables enterprises to discover, document, and manage every AI system from a single interface, transforming a chaotic "jungle of AI systems" into a controlled, auditable, and compliant environment. The platform is particularly vital for sectors like finance and healthcare, where stringent regulations such as the EU AI Act demand rigorous accountability and transparency. By integrating flexible onboarding, real-time monitoring, explainability, and automated compliance workflows, Deeploy empowers organizations to scale their AI initiatives with confidence, ensuring innovation is balanced with responsibility and trust.
About Threat Watch
Threat Watch is a cutting-edge cybersecurity intelligence solution designed to empower organizations by providing a comprehensive overview of their cyber health. This innovative tool meticulously analyzes an organization's digital assets, vulnerabilities, and exposures, enabling users to swiftly identify and address potential risks. By leveraging real-time insights and automated assessments, Threat Watch offers a clear picture of security threats, allowing businesses to prioritize and mitigate risks effectively. It is particularly beneficial for IT professionals, cybersecurity teams, and organizational leaders who seek to bolster their defenses against ever-evolving cyber threats. With its robust capabilities, Threat Watch not only uncovers critical security issues but also enhances the overall cybersecurity posture of any organization, making it an indispensable asset in today’s digital landscape. By focusing on essential security categories such as compromised credentials, breached accounts, and dark web content, Threat Watch ensures that organizations can respond proactively to cybersecurity challenges, ultimately safeguarding their operational integrity and protecting sensitive data.
Frequently Asked Questions
Deeploy FAQ
How does Deeploy help with the EU AI Act?
Deeploy is specifically engineered to address the core requirements of the EU AI Act. It provides tools for mandatory AI system inventory creation, risk classification based on the Act's categories, and implementation of corresponding conformity measures. The platform's automated evidence collection and audit trails generate the necessary documentation for compliance assessments. Its real-time monitoring and explainability features directly support the Act's mandates for transparency and human oversight, particularly for high-risk AI systems.
Can Deeploy integrate with our existing MLOps and AI vendor platforms?
Yes, a core strength of Deeploy is its flexible integration capability. It is designed to connect with any major MLOps platform (e.g., MLflow, Sagemaker) and GenAI vendor APIs without requiring you to migrate your existing workflows. This "connect-first" approach allows you to maintain your current tech stack while adding a centralized governance layer on top, eliminating blind spots and bringing all AI activities under a single pane of glass for management and oversight.
What is meant by "explainability" in Deeploy?
Explainability in Deeploy refers to the platform's ability to make AI model decisions interpretable to humans. For traditional machine learning models, it provides techniques like feature importance scores to show which input factors most influenced a specific prediction. For Large Language Models (LLMs), it offers tracing and output analysis. This transparency is crucial for debugging models, building trust with end-users, fulfilling regulatory "right to explanation" clauses, and enabling subject matter experts to provide meaningful feedback to improve system performance.
Who are the primary users of Deeploy within an organization?
Deeploy serves a cross-functional audience. AI Governance & Risk Officers use it to set policies and ensure compliance. Data Science & MLOps Engineers use it to deploy models and implement controls. Business Leaders & Product Managers rely on its dashboards for visibility into AI performance and risk. Legal & Compliance Teams utilize its automated documentation for audits. This multi-user design ensures governance is a collaborative, integrated process rather than a standalone compliance checkpoint.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, including small businesses, large enterprises, and government agencies. Any entity that prioritizes cybersecurity can leverage its features to enhance their cyber health.
How does Threat Watch monitor the dark web?
Threat Watch employs advanced algorithms and data mining techniques to continuously scan the dark web for compromised accounts and credentials. This proactive monitoring helps organizations stay informed about potential threats to their data.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to complement existing cybersecurity solutions. Its integration capabilities allow organizations to enhance their security framework without disrupting current workflows.
Is Threat Watch easy to use for non-technical users?
Absolutely. Threat Watch features an intuitive user interface that makes it accessible to both technical and non-technical users. Comprehensive dashboards and reports simplify complex data, enabling informed decision-making for all stakeholders.
Alternatives
Deeploy Alternatives
Deeploy is an AI governance platform within the business intelligence and compliance software category. It provides organizations with a centralized system for managing oversight, compliance, and risk across their AI initiatives, which is increasingly critical under regulations like the EU AI Act. Organizations may seek alternatives to Deeploy for various reasons. Common considerations include budget constraints and specific pricing models, the need for different feature sets or deeper integrations with existing MLOps tools, and platform requirements such as deployment options (SaaS vs. on-premise) or scalability needs for very large or complex AI portfolios. When evaluating an alternative AI governance solution, key factors to assess include the platform's ability to provide comprehensive visibility and automated discovery of AI models, its support for relevant regulatory frameworks and customizable controls, and the depth of its monitoring, explainability, and audit trail capabilities. The ideal solution should reduce manual compliance overhead while integrating smoothly into your existing technology stack.
Threat Watch Alternatives
Threat Watch is a state-of-the-art cybersecurity intelligence solution that falls within the realm of business intelligence, specifically tailored to enhance an organization's cybersecurity health. This tool offers a comprehensive overview of digital assets, vulnerabilities, and exposures, enabling IT professionals and organizational leaders to quickly identify and mitigate potential risks. Users commonly seek alternatives to Threat Watch due to various factors, including pricing, feature sets, and specific platform needs that may not be fully addressed by the product. When considering alternatives, it's crucial to evaluate the capabilities of each solution, such as real-time risk assessments, automated vulnerability scanning, and comprehensive reporting, ensuring that they align with the unique security requirements of your organization. --- [{"question": "What is Threat Watch?", "answer": "Threat Watch is a cybersecurity intelligence solution that helps organizations assess and enhance their cybersecurity health by providing real-time insights into vulnerabilities and threats."},{"question": "Who is Threat Watch for?", "answer": "Threat Watch is designed for IT professionals, cybersecurity teams, and organizational leaders who aim to improve their defenses against evolving cyber threats."},{"question": "Is Threat Watch free?", "answer": "Threat Watch is a premium service, and pricing details can vary based on the specific needs and scale of the organization."},{"question": "What are the main features of Threat Watch?", "answer": "Main features of Threat Watch include real-time risk assessment, automated vulnerability scanning, dark web monitoring, and comprehensive reporting."}]
