CMMC ROI vs Threat Watch
Side-by-side comparison to help you choose the right product.
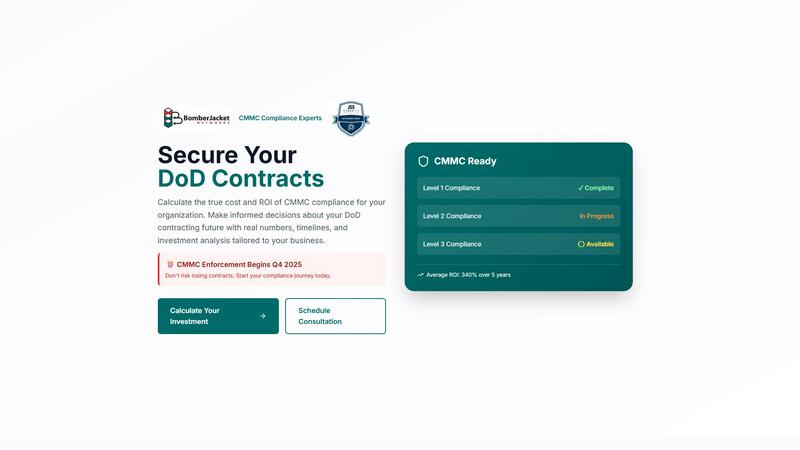
CMMC ROI
CMMC ROI empowers organizations to assess compliance costs and ROI, ensuring informed decisions for securing DoD.
Last updated: March 1, 2026
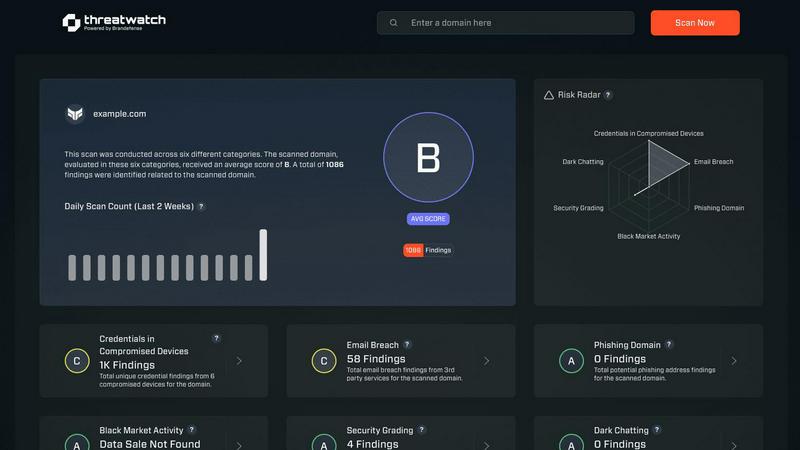
Threat Watch
Threat Watch provides rapid insights to evaluate and strengthen your cybersecurity posture across essential security.
Last updated: March 1, 2026
Visual Comparison
CMMC ROI
Threat Watch
Feature Comparison
CMMC ROI
Comprehensive ROI Analysis
CMMC ROI calculates the true cost of compliance, allowing organizations to understand their financial commitment over a five-year horizon. This analysis includes implementation costs, maintenance, and recertification expenses, providing a clear financial picture.
Tailored Compliance Strategies
The tool offers personalized recommendations based on the organization's size, industry, and current compliance status. This customization ensures that businesses receive relevant guidance that aligns with their specific needs and goals.
Investment Calculator
CMMC ROI features an intuitive investment calculator that allows contractors to input their data and receive tailored ROI estimates. This empowers users to assess potential costs and returns, facilitating informed decision-making.
Progress Tracking
The solution includes a built-in progress tracking feature that monitors compliance status and milestones. This allows organizations to visualize their journey toward certification and adjust their strategies as needed, ensuring timely compliance.
Threat Watch
Comprehensive Security Analysis
Threat Watch provides an in-depth analysis of an organization's cybersecurity landscape. It evaluates critical security categories, ensuring users gain a holistic view of their security posture and can effectively identify vulnerabilities.
Real-Time Insights
With its real-time data monitoring capabilities, Threat Watch empowers organizations to stay ahead of potential threats. Users receive immediate alerts about security issues, allowing for timely responses to mitigate risks.
Automated Risk Assessments
The platform automates the process of risk assessments, significantly reducing the workload on cybersecurity teams. This feature enables organizations to conduct regular evaluations without extensive manual effort, ensuring continuous security oversight.
Dark Web Monitoring
Threat Watch actively monitors the dark web for compromised credentials and sensitive data. By identifying potential breaches and unauthorized access to information, organizations can take swift action to protect their assets.
Use Cases
CMMC ROI
Small Contractors Seeking Compliance
Small contractors with limited resources can utilize CMMC ROI to identify the most cost-effective pathways to compliance. By understanding their investment and potential ROI, they can make strategic business decisions that align with their financial capabilities.
Medium to Large Enterprises
Medium to large contractors can leverage CMMC ROI to manage extensive compliance requirements. The tool provides insights into the financial implications of achieving higher CMMC levels, helping these organizations allocate resources efficiently.
Organizations in the DoD Supply Chain
Companies within the DoD supply chain can use CMMC ROI to assess the risks associated with non-compliance. By calculating potential losses and comparing them to compliance costs, organizations can prioritize investments that protect their contracts.
Technology Firms Transitioning to CMMC
Technology firms that offer services to DoD contractors can utilize CMMC ROI to prepare their clients for upcoming compliance requirements. By offering insights into the costs and benefits of CMMC certification, these firms can position themselves as valuable partners in the compliance journey.
Threat Watch
Proactive Threat Detection
Organizations can utilize Threat Watch to implement proactive threat detection strategies. By regularly monitoring their digital assets, they can identify vulnerabilities before they are exploited, thereby enhancing their overall security.
Incident Response Planning
Threat Watch aids in developing effective incident response plans. By understanding the landscape of potential threats, organizations can prepare and implement strategies to minimize damage in the event of a cybersecurity incident.
Compliance and Regulatory Requirements
Many organizations face stringent compliance and regulatory requirements regarding data protection. Threat Watch helps ensure that organizations meet these requirements by providing comprehensive assessments of their cybersecurity health.
Enhanced Security Training
IT teams can leverage insights from Threat Watch to inform security training initiatives. By understanding the most common vulnerabilities and threats, organizations can better educate employees on best practices and security awareness.
Overview
About CMMC ROI
CMMC ROI is a specialized solution crafted for Department of Defense (DoD) contractors who face the intricate challenges of achieving Cybersecurity Maturity Model Certification (CMMC) compliance. Developed by BomberJacket Networks, this tool provides an essential framework that not only navigates the compliance landscape but also focuses on delivering a strong return on investment (ROI). With over 20 years of cybersecurity experience and a remarkable 99% success rate, CMMC ROI equips organizations with the ability to evaluate their compliance requirements thoroughly. By calculating the true costs associated with CMMC certification, contractors can make informed, data-driven decisions about their future in DoD contracting. As CMMC enforcement is set to begin in Q4 2025, ensuring compliance has never been more critical for maintaining competitiveness and securing lucrative government contracts. CMMC ROI empowers organizations to proactively address compliance needs, thereby safeguarding their interests and enhancing their market position.
About Threat Watch
Threat Watch is a cutting-edge cybersecurity intelligence solution designed to empower organizations by providing a comprehensive overview of their cyber health. This innovative tool meticulously analyzes an organization's digital assets, vulnerabilities, and exposures, enabling users to swiftly identify and address potential risks. By leveraging real-time insights and automated assessments, Threat Watch offers a clear picture of security threats, allowing businesses to prioritize and mitigate risks effectively. It is particularly beneficial for IT professionals, cybersecurity teams, and organizational leaders who seek to bolster their defenses against ever-evolving cyber threats. With its robust capabilities, Threat Watch not only uncovers critical security issues but also enhances the overall cybersecurity posture of any organization, making it an indispensable asset in today’s digital landscape. By focusing on essential security categories such as compromised credentials, breached accounts, and dark web content, Threat Watch ensures that organizations can respond proactively to cybersecurity challenges, ultimately safeguarding their operational integrity and protecting sensitive data.
Frequently Asked Questions
CMMC ROI FAQ
What is CMMC ROI and how does it help contractors?
CMMC ROI is a tool designed to assist DoD contractors in achieving compliance with the Cybersecurity Maturity Model Certification. It provides detailed cost analysis and ROI projections to inform strategic decision-making regarding compliance investments.
How does the investment calculator work?
The investment calculator allows users to input specific data related to their organization, such as size, current compliance status, and expected DoD revenue. It then generates tailored ROI estimates and investment costs, making it easier for contractors to plan their compliance journey.
What are the benefits of achieving CMMC certification?
Achieving CMMC certification significantly reduces the risk of losing government contracts due to non-compliance. It also enhances win rates against competitors, protects against breaches and false claims, and improves overall cybersecurity posture.
How long does it take to achieve CMMC Level 2 certification?
The implementation timeline for achieving CMMC Level 2 certification typically spans 12 months. This includes stages such as gap assessments, remediation, documentation, preparation for audits, and the final certification assessment.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, including small businesses, large enterprises, and government agencies. Any entity that prioritizes cybersecurity can leverage its features to enhance their cyber health.
How does Threat Watch monitor the dark web?
Threat Watch employs advanced algorithms and data mining techniques to continuously scan the dark web for compromised accounts and credentials. This proactive monitoring helps organizations stay informed about potential threats to their data.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to complement existing cybersecurity solutions. Its integration capabilities allow organizations to enhance their security framework without disrupting current workflows.
Is Threat Watch easy to use for non-technical users?
Absolutely. Threat Watch features an intuitive user interface that makes it accessible to both technical and non-technical users. Comprehensive dashboards and reports simplify complex data, enabling informed decision-making for all stakeholders.
Alternatives
CMMC ROI Alternatives
CMMC ROI is a specialized solution that assists Department of Defense (DoD) contractors in calculating compliance costs and return on investment (ROI) related to Cybersecurity Maturity Model Certification (CMMC). As a part of BomberJacket Networks' suite of business intelligence services, it offers organizations a comprehensive strategy for navigating the intricacies of CMMC compliance while securing government contracts. Users often seek alternatives due to factors such as pricing, specific feature sets, and compatibility with their existing platforms. When searching for an alternative, it is essential to consider the comprehensiveness of the investment analysis, the accuracy of ROI projections, and the overall value that aligns with your organization's compliance goals.
Threat Watch Alternatives
Threat Watch is a state-of-the-art cybersecurity intelligence solution that falls within the realm of business intelligence, specifically tailored to enhance an organization's cybersecurity health. This tool offers a comprehensive overview of digital assets, vulnerabilities, and exposures, enabling IT professionals and organizational leaders to quickly identify and mitigate potential risks. Users commonly seek alternatives to Threat Watch due to various factors, including pricing, feature sets, and specific platform needs that may not be fully addressed by the product. When considering alternatives, it's crucial to evaluate the capabilities of each solution, such as real-time risk assessments, automated vulnerability scanning, and comprehensive reporting, ensuring that they align with the unique security requirements of your organization. --- [{"question": "What is Threat Watch?", "answer": "Threat Watch is a cybersecurity intelligence solution that helps organizations assess and enhance their cybersecurity health by providing real-time insights into vulnerabilities and threats."},{"question": "Who is Threat Watch for?", "answer": "Threat Watch is designed for IT professionals, cybersecurity teams, and organizational leaders who aim to improve their defenses against evolving cyber threats."},{"question": "Is Threat Watch free?", "answer": "Threat Watch is a premium service, and pricing details can vary based on the specific needs and scale of the organization."},{"question": "What are the main features of Threat Watch?", "answer": "Main features of Threat Watch include real-time risk assessment, automated vulnerability scanning, dark web monitoring, and comprehensive reporting."}]
