AutoPhish vs Decode This Text
Side-by-side comparison to help you choose the right product.
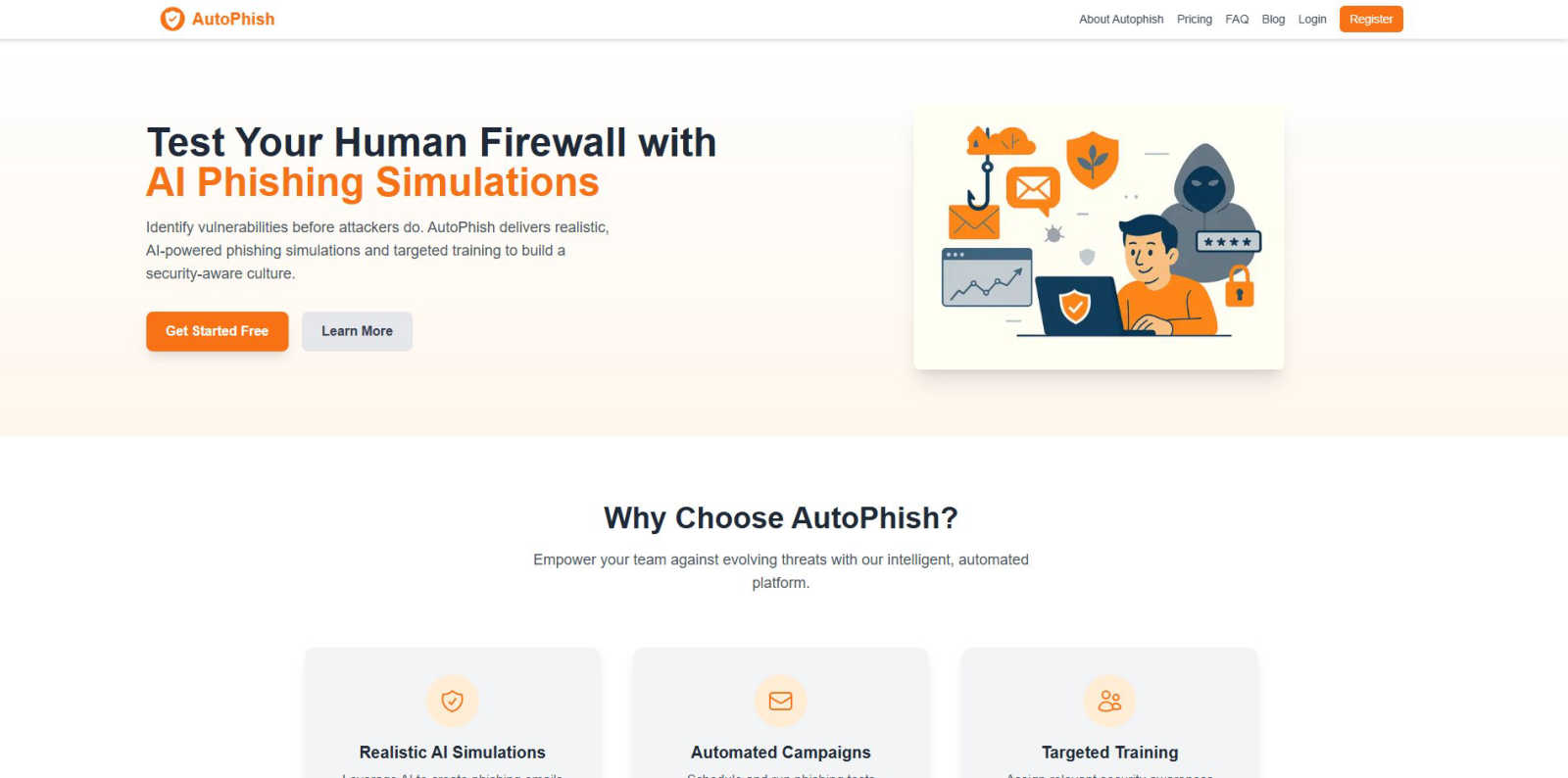
AutoPhish uses AI to run automated phishing simulations and provide targeted security training.
Last updated: March 1, 2026
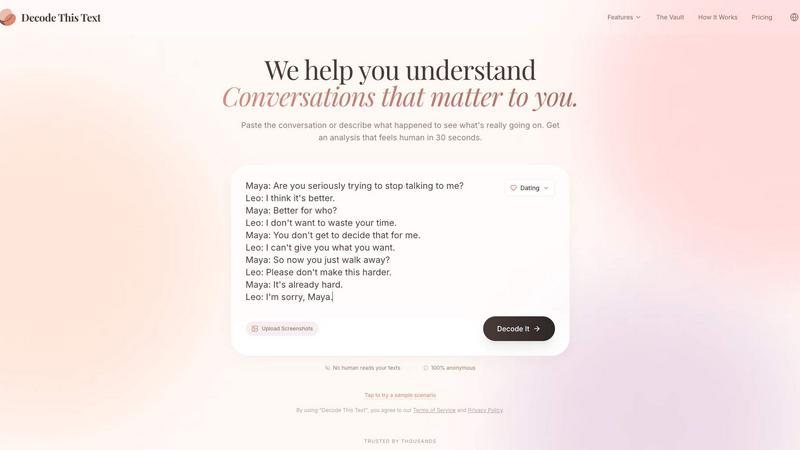
Decode This Text
Decode This Text provides quick, human-like analyses of conversations in just 30 seconds for ultimate clarity and.
Last updated: February 28, 2026
Visual Comparison
AutoPhish
Decode This Text
Feature Comparison
AutoPhish
Realistic AI-Powered Phishing Simulations
AutoPhish utilizes sophisticated AI algorithms to create phishing email templates that are virtually indistinguishable from genuine malicious campaigns. The AI analyzes current threat intelligence and common social engineering lures to generate content that evolves with the threat landscape. This ensures simulations are not based on static, recognizable templates but are dynamic and highly relevant, providing a true test of an employee's vigilance and preparedness against sophisticated attacks.
Automated Campaign Management
The platform allows security administrators to fully automate their phishing simulation programs. Users can configure campaigns by selecting AI-generated templates, defining target employee groups, and setting precise schedules for deployment. This automation eliminates manual overhead, ensures consistent and regular testing intervals (a key factor in retention, as noted in SANS Institute research), and allows security teams to focus on strategic analysis and remediation rather than operational tasks.
Targeted, Role-Based Training Modules
Following each simulation, AutoPhish provides detailed analytics on user interactions. The platform then automatically assigns customized security awareness training modules based on individual performance and the user's specific role within the organization. For instance, a finance department employee who clicks a simulated invoice scam would receive different training than an HR employee who fails a credential-harvesting test, ensuring education is contextually relevant and maximally effective.
Comprehensive Reporting & Analytics Dashboard
AutoPhish offers an advanced reporting suite that delivers deep insights into organizational vulnerability. The dashboard provides metrics such as click-through rates, time-to-click, and repeat offender identification, all presented in an intuitive format. This data empowers security leaders to quantify risk, measure the ROI of their awareness programs, track improvement over time, and make informed decisions about where to allocate additional security resources and training focus.
Decode This Text
Comprehensive Analysis
Decode This Text offers a thorough examination of messages, highlighting emotional tones, intentions, and contextual elements. This feature ensures that users grasp the nuances behind any communication, enabling them to respond appropriately.
Visual Input Capability
Users can conveniently upload screenshots of conversations, allowing the tool to analyze the text without requiring manual input. This feature simplifies the process for those who prefer visual communication, making it easier to decode complex interactions.
Emotional Tone Detection
This feature assesses the emotional temperature of messages, categorizing them as cold, sarcastic, or friendly. By understanding the emotional context, users can avoid misinterpretations and respond in a manner that aligns with the sender's mood.
Response Suggestions
For users unsure about how to reply, Decode This Text provides three tailored response options—calm, direct, or firm. This feature equips users with the confidence to engage in conversations effectively, regardless of the message's complexity.
Use Cases
AutoPhish
Proactive Security Posture Assessment for IT & Security Teams
Security administrators use AutoPhish to conduct regular, controlled phishing tests to baseline and continuously monitor the organization's human risk surface. By identifying which departments or individuals are most susceptible to specific attack vectors, they can prioritize resources, tailor communication, and demonstrate tangible risk metrics to executive leadership, thereby justifying further cybersecurity investments and shaping security policy.
Compliance and Audit Readiness
Organizations in regulated industries (e.g., finance, healthcare) leverage AutoPhish to fulfill mandatory security awareness training requirements for standards like ISO 27001, SOC 2, GDPR, and HIPAA. The platform provides documented proof of ongoing employee testing and training, creating an audit trail that demonstrates due diligence in cultivating a security-aware workforce, which is a critical component of regulatory compliance frameworks.
Onboarding and Continuous Employee Education
HR and People Operations teams integrate AutoPhish into the employee onboarding process to establish security fundamentals from day one. Furthermore, they use the platform's automated scheduling to deliver continuous, bite-sized training simulations throughout the year. This constant reinforcement helps combat "security fatigue" and keeps cybersecurity top-of-mind, embedding safe practices into the company culture.
Simulating Sophisticated Supply Chain & Whaling Attacks
Beyond generic phishing, AutoPhish enables organizations to simulate advanced persistent threats (APTs) like whaling (targeting executives) or supply chain compromise emails. Security teams can craft highly targeted campaigns against leadership or specific partners to test defenses against these high-impact, low-frequency attacks, ensuring that even the most sophisticated social engineering attempts can be identified and reported.
Decode This Text
Navigating Ambiguous Texts
Decode This Text is invaluable when dealing with vague texts from friends or colleagues. By providing a clear interpretation, users can avoid unnecessary confusion and maintain healthy communication.
Professional Email Clarification
In the workplace, ambiguous emails can lead to miscommunication. This tool helps users decipher the true meaning behind brief or unclear messages, ensuring that responses are appropriate and informed.
Family Communication Enhancement
Family dynamics can be complicated by misunderstandings. Decode This Text assists users in interpreting family messages, promoting better understanding and reducing potential conflicts.
Relationship Insights
For those in romantic relationships, Decode This Text can help clarify intentions behind messages that may seem evasive or confusing. This insight fosters healthier conversations and strengthens connections.
Overview
About AutoPhish
AutoPhish is an advanced, AI-powered cybersecurity platform specifically engineered to fortify an organization's human firewall through realistic phishing simulations and targeted security awareness training. The platform addresses a critical vulnerability: human error, which is implicated in over 74% of all data breaches according to Verizon's 2024 Data Breach Investigations Report. By leveraging cutting-edge artificial intelligence, AutoPhish generates highly convincing phishing emails that meticulously mimic the tactics, techniques, and procedures (TTPs) of real-world attackers, tailored to the specific context and industry of the target organization. This solution is designed for businesses of all sizes, from SMBs to large enterprises, that seek a proactive, data-driven approach to cybersecurity risk management. Its core value proposition lies in transforming employees from potential security liabilities into informed, vigilant defenders. By automating the entire lifecycle of phishing testing—from campaign configuration and scheduling to detailed analytics and personalized training assignment—AutoPhish enables security teams to efficiently build a resilient, security-aware culture, identify at-risk individuals, and measurably reduce the likelihood of successful phishing attacks.
About Decode This Text
Decode This Text is a cutting-edge communication tool designed to assist users in unraveling the often ambiguous meanings behind various messages. Whether you're struggling to interpret a cryptic email from your boss, a vague text from a friend, or a confusing message from a client, this innovative tool provides essential clarity. By simply pasting the text or describing the context, users receive an insightful analysis of the sender's underlying intentions, emotional tone, and appropriate response strategies. This tool is particularly beneficial for anyone looking to enhance their communication skills, foster better relationships, and eliminate misunderstandings. With a user-friendly interface and rapid analysis, Decode This Text empowers you to navigate your interactions confidently, alleviating the stress of overanalyzing every word.
Frequently Asked Questions
AutoPhish FAQ
How realistic are the AutoPhish simulations?
AutoPhish simulations are highly realistic, powered by AI that continuously learns from global phishing trends and threat actor methodologies. The platform generates emails with convincing sender spoofing, contextual content tailored to your industry, and persuasive language designed to bypass standard scrutiny. This level of realism is crucial for accurate assessment, as studies show that traditional, obvious phishing tests do not adequately prepare employees for modern, sophisticated attacks.
Is it safe to send simulated phishing emails to my employees?
Yes. AutoPhish is designed with safety and ethics as core principles. The platform requires you to verify domain ownership, ensuring simulations are sent from an authorized source and do not interact with external malicious infrastructure. All simulated links lead to safe, internal educational pages, and the system includes safeguards to prevent targeting individuals who have opted out. Transparency with employees about the program's educational purpose is also strongly recommended.
What happens if an employee fails a phishing test?
When an employee interacts with a simulated phishing email (e.g., clicks a link), they are immediately directed to a friendly, instructive landing page that explains the simulation and what cues they missed. Subsequently, AutoPhish's system can automatically enroll them in a targeted training module relevant to the attack vector they fell for. This "teachable moment" approach is proven by academic research to significantly improve long-term retention compared to punitive measures.
Can AutoPhish help with email domain security?
Absolutely. AutoPhish offers a free DNS Security Check tool that analyzes your domain's email authentication records (SPF, DKIM, DMARC). Proper configuration of these protocols is essential to prevent domain spoofing, a common tactic in real phishing attacks. The tool provides an instant security score, detailed analysis, and actionable recommendations to harden your email ecosystem, complementing the human-focused training of the core platform.
Decode This Text FAQ
How does Decode This Text ensure user privacy?
Decode This Text guarantees 100% anonymity. No human reads your texts, ensuring that your conversations remain private and secure.
What types of messages can I analyze with Decode This Text?
You can analyze any written communication, including text messages, emails, and social media messages. The tool is designed to handle a wide variety of contexts and formats.
How quickly can I expect to receive an analysis?
The tool typically provides a comprehensive analysis within 30 seconds, allowing users to gain clarity rapidly and respond in a timely manner.
Is there any limit to the number of messages I can decode?
Currently, there is no specified limit on the number of messages you can analyze. Users can decode as many conversations as they need to enhance their communication skills.
Alternatives
AutoPhish Alternatives
AutoPhish is a specialized Business Intelligence and Productivity platform that leverages AI to automate phishing simulations and deliver targeted security awareness training. Organizations implement such tools to proactively build a human firewall against one of the most prevalent cyber threats. Users may explore alternatives to AutoPhish for various strategic reasons. Common drivers include budget constraints, the need for different feature sets like more extensive compliance reporting or third-party integrations, and platform-specific requirements such as on-premises deployment or a preference for a different vendor ecosystem within their existing security stack. When evaluating an alternative solution, key considerations should include the realism and adaptability of its simulated attacks, the depth and customization of its training content, the robustness of analytics and reporting, and the overall total cost of ownership. The goal is to select a platform that not only tests employee vigilance but also effectively educates and changes long-term security behavior.
Decode This Text Alternatives
Decode This Text is an innovative tool in the productivity and management category, designed to help users decipher the true meanings behind confusing conversations. By providing quick, human-like analyses of messages, it offers insights that can enhance understanding and communication. Users often seek alternatives to Decode This Text for various reasons, including pricing concerns, feature sets, specific platform compatibility, or personal preferences in user interface design. When selecting an alternative, it's essential to consider factors such as the depth of analysis provided, user-friendliness, response time, and whether the tool meets your specific communication needs. Additionally, evaluating customer support options and user reviews can offer insight into the effectiveness and reliability of the alternative tool, ensuring that it aligns with your expectations.

